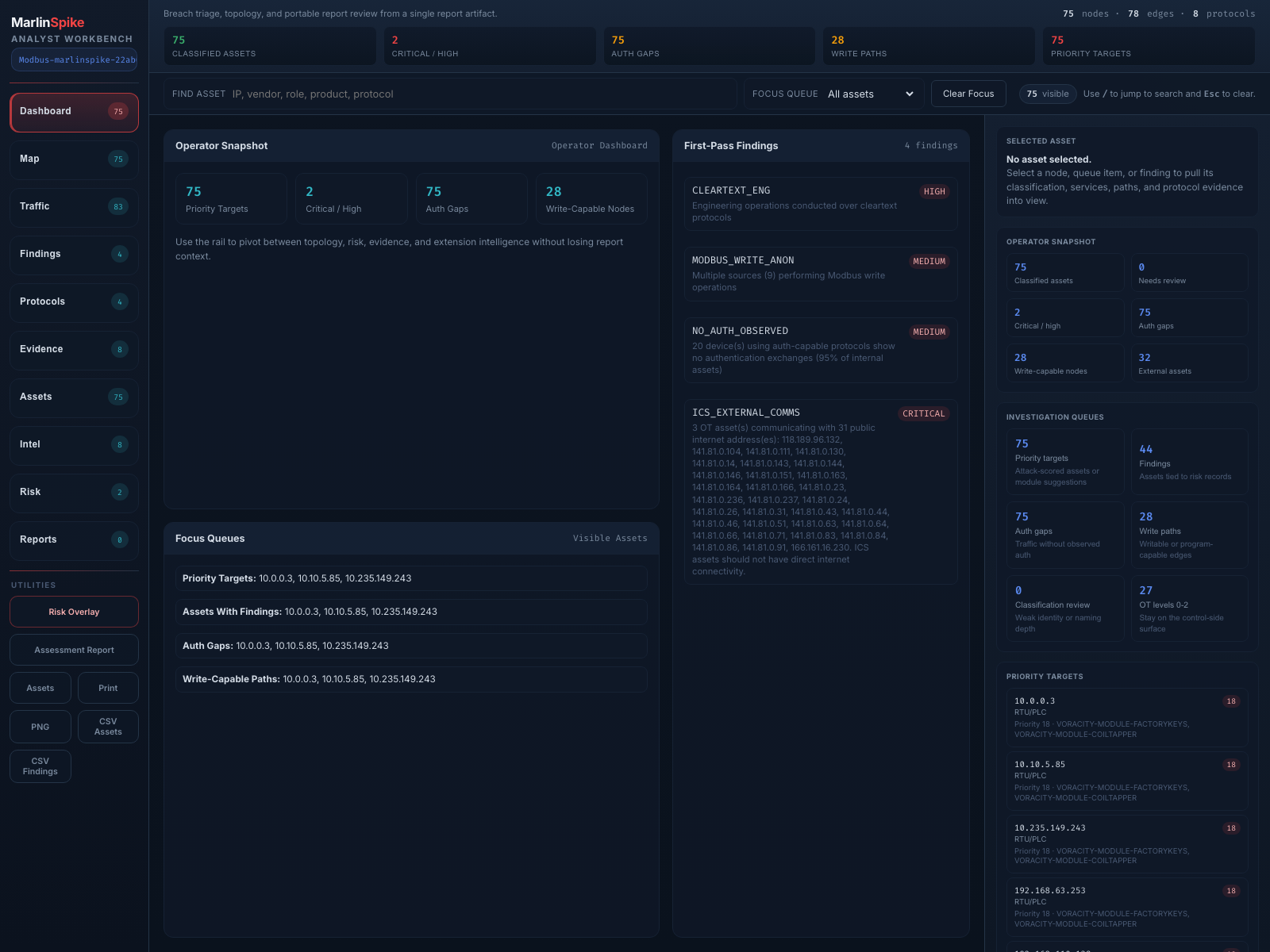
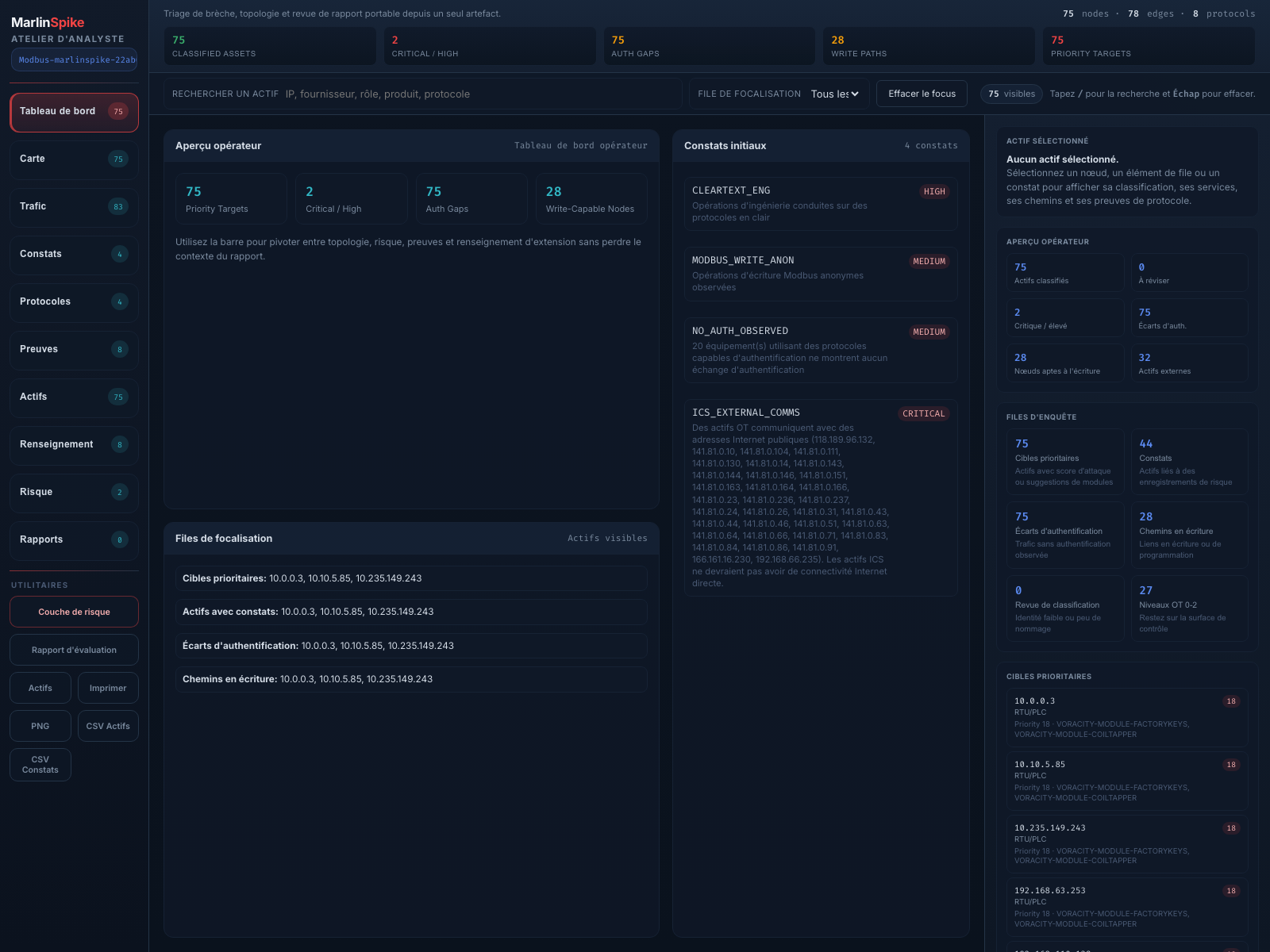
Passive OT/ICS topology workbench
Feed it pcap or pcapng, keep packet transmission at zero, and review topology, asset context, cross-Purdue paths, suspicious external comms, and portable JSON reports — with the team.
Map-first workbench, multi-lens relational graphing.
A persistent map canvas with a lens chip strip on top, a dockable inspector on the right, and a slide-up drawer with seven tabbed tables at the bottom. Six lenses re-render the map: Comms, Findings, IOC, ATT&CK, Baseline, and Peers — all derived from a single 12-entity / 12-relationship taxonomy.
What MarlinSpike commits to.
Six non-negotiable principles derived from the realities of passive OT/ICS analysis on real engagement hosts. They shape every release.
OT-Native, Not Adapted
Shared Workbench, Not Single-User
The Report Is the Contract
Field-Deployable Footprint
Bilingual by Default
Three jobs MarlinSpike was built for.
Topology reconstruction, responder triage, and longitudinal asset baselines — in one shared workbench, fed by passive captures.
Topology reconstruction
Responder triage
Longitudinal baselines
The key understanding
MarlinSpike isn't a desktop analyzer. It's a temporary on-site workbench for OT engagements — drop it on an engagement host, share the URL, triage together, hand off the JSON report.
Four surfaces that turn "the workbench found something" into something you can act on.
The v3.x line is built around closing the gap between analysis and action. Every release adds another link in the spotted-it→opened-it loop.
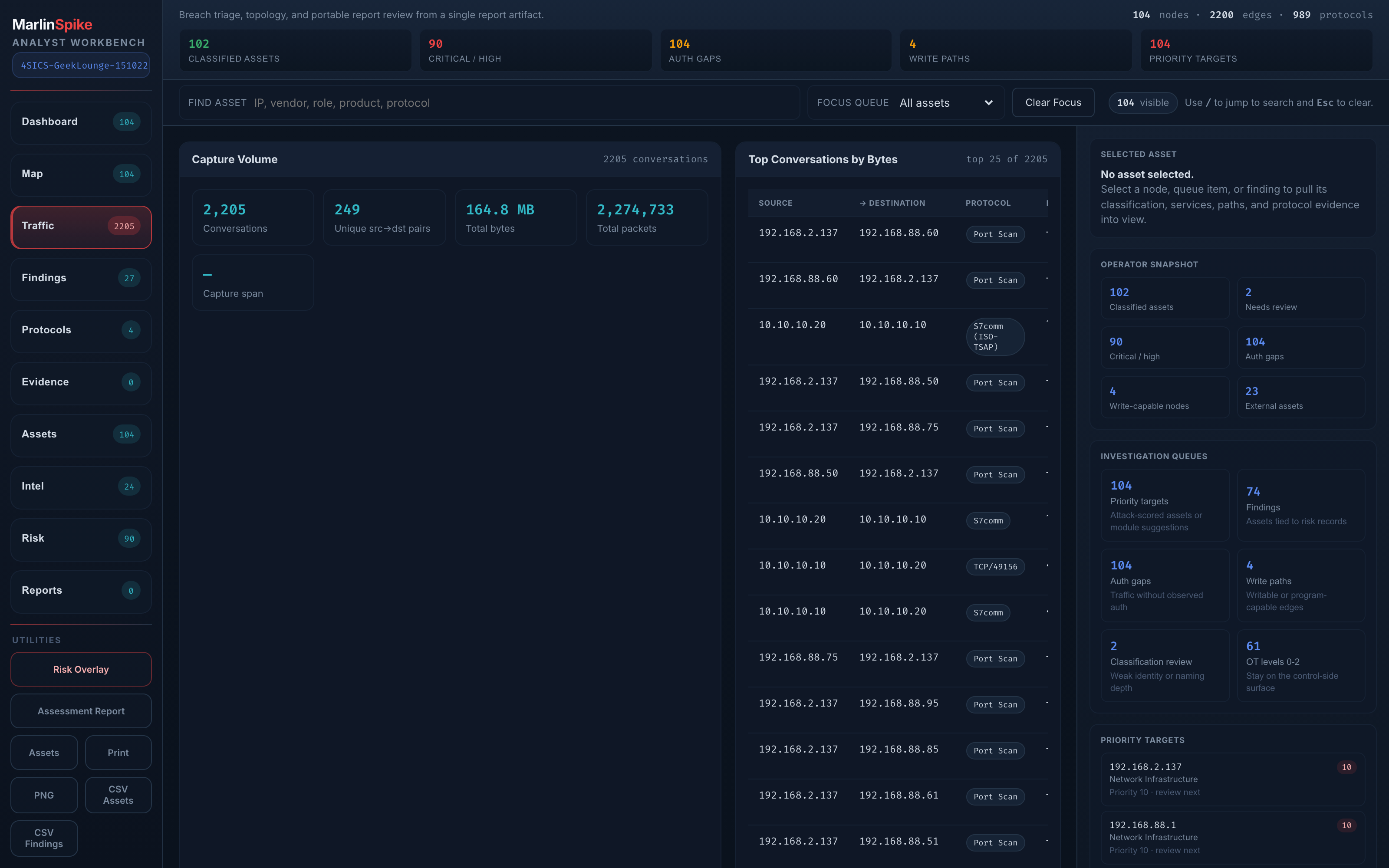
Time scrubbing + sub-PCAP carve-out
- Adaptive packet-rate histogram below the workbench toolbar
- Drag a time window — every conversation pane filters live to that range
- Per-row Extract button shells out to tshark + editcap, downloads pcap
- From "spotted it" to "open it in Wireshark" is two clicks
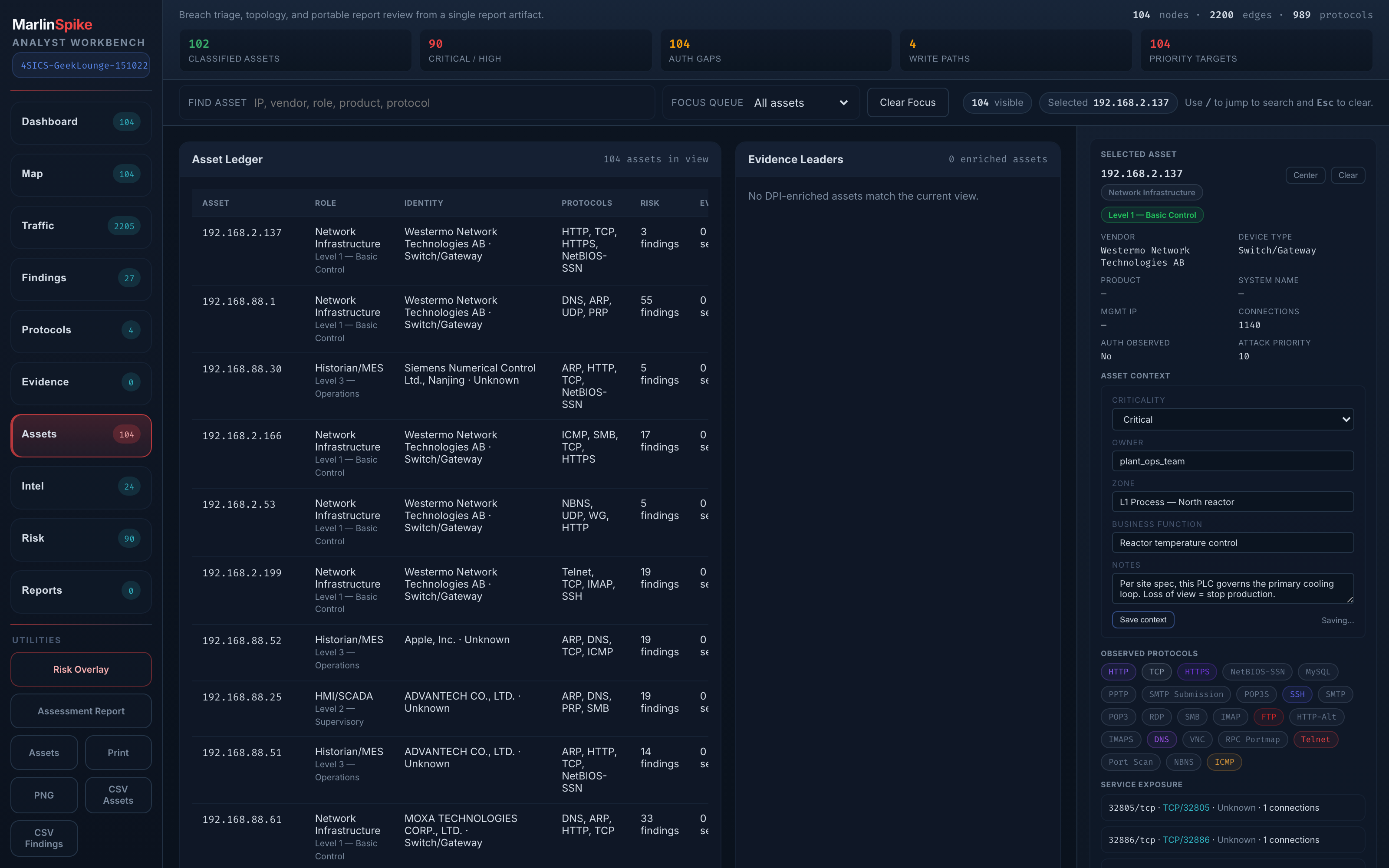
Asset context with contextual severity
- Tag every asset with owner, criticality, zone, business function, free-text notes
- Project-scoped, MAC-first / IP-fallback key
- MEDIUM on a safety controller can outrank CRITICAL on a print server
- Per-finding notes (status + body) travel with the project across reports
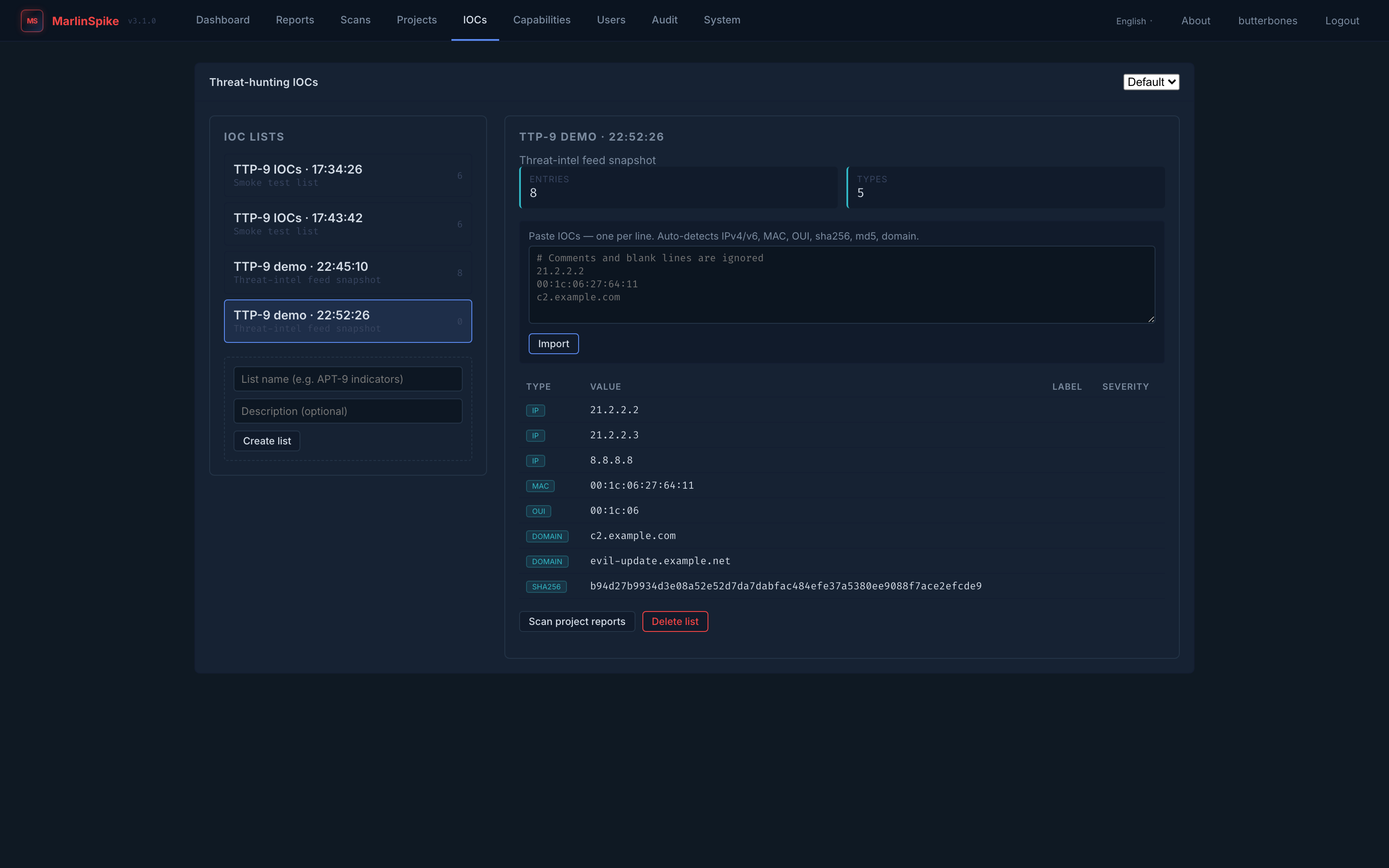
IOC threat-hunting across every report
/iocs page is a paste-and-scan workflow. STIX / MISP import is on the roadmap; the paste-list MVP is live.
- Paste-bulk import auto-detects IPv4/v6, MAC, OUI, sha256, md5, domains
- Scan project reports walks every report — nodes, conversations, c2, DNS, malware findings
- Per-IOC severity rollups and per-report match locations
- Project-scoped lists, persistent across runs
Live ATT&CK matrix from passive observations
- Tactic-grouped technique grid (ICS + Enterprise domains)
- Sourced from the marlinspike-mitre plugin output, not hand-curated
- Sub-techniques, mitigations, and response guidance per finding
- Click any technique → pivot to the findings that triggered it
Bilingual workbench, more languages coming
- Every screen flips between English and Français — including engine-emitted finding categories, descriptions, and remediations
- Locale picker in the nav, session-persisted, with Accept-Language fallback
- Homegrown JSON-dictionary i18n layer — no new pip dependencies
- Additional locales planned; the dictionary structure makes new languages additive, not a refactor
Built for the people who actually triage.
MarlinSpike is the open-source core behind Fathom. It exists to be useful to working OT/ICS responders, not just systems programmers.
To responders
To OT engineers
To integrators
pip install marlinspike exposes create_app and db. Three formal extension surfaces: Rust engines, Python plugins, YAML rule packs.
Start with the wiki, ship a Docker stack, share a URL.
No license dance, no vendor onboarding call. Five minutes from git clone to a working workbench at 127.0.0.1:5001.